- Morris Clayton, Morris Invest (YouTube); Pfc. Sandoval, Seth Auberon (eds.), Wisdom Quarterly
Monday, July 22, 2024
System of a down: US state of emergency
Friday, September 4, 2020
Comedian Jimmy Dore goes spiritual (video)
Jim Dore evolves, talks about New Age spirituality, psychology, and Mahayana Buddhism/Hinduism.
Tuesday, May 2, 2017
Wednesday, December 4, 2013
NSA infects 50,000 computer networks
 |
| The NSA or National Security Agency spies legally and illegally (Corbis/NRC.nl) |
 The American intelligence service -- NSA --
infected more than 50,000 computer networks worldwide with malicious
software designed to steal sensitive information.
The American intelligence service -- NSA --
infected more than 50,000 computer networks worldwide with malicious
software designed to steal sensitive information. Friday, March 29, 2013
Being spied on in America (audio)
 It's legal for the government to read emails that are six months and older -- without a warrant, without probable cause, without a citizen ever knowing it. This is known because the government wants to expand that to earlier emails. National Security Letters are enough. Why bother with a rubber stamp from a FISA court?
It's legal for the government to read emails that are six months and older -- without a warrant, without probable cause, without a citizen ever knowing it. This is known because the government wants to expand that to earlier emails. National Security Letters are enough. Why bother with a rubber stamp from a FISA court?Friday, June 1, 2012
Stuxnet: Obama, Israel attacked Iran (cartoon)
 (thismodernworld.org)
(thismodernworld.org)Obama, Israel ordered computer attacks on Iran
 The Stuxnet worm, developed by U.S. and Israeli agencies, targeted Iran's nuclear program, says the New York Times.
The Stuxnet worm, developed by U.S. and Israeli agencies, targeted Iran's nuclear program, says the New York Times.(IDG) U.S. President Barack Obama ordered the Stuxnet cyberattacks on Iran in an effort to slow the country's development of a nuclear program, according to a report in The New York Times.
 Quoting anonymous sources, the Times reported that in the early days of his presidency, Obama accelerated attacks related to an effort begun by the George W. Bush administration. The Stuxnet worm, long rumored to have been developed by Israel or the U.S., escaped from Iranian computers in mid-2010 and compromised computers across the Internet.
Quoting anonymous sources, the Times reported that in the early days of his presidency, Obama accelerated attacks related to an effort begun by the George W. Bush administration. The Stuxnet worm, long rumored to have been developed by Israel or the U.S., escaped from Iranian computers in mid-2010 and compromised computers across the Internet.
Obama considered shutting down the cyberattacks after Stuxnet began compromising other computers, but decided to continue with the program, according to the Times. The Stuxnet worm came from a joint U.S. and Israeli effort to target the Iranian nuclear program, the Times said. The newspaper interviewed U.S., Israeli and European officials currently and formerly involved with the cyberattack program, it said. More
 One Per Cent: Obama "gave full backing to Stuxnet attack on Iran"
One Per Cent: Obama "gave full backing to Stuxnet attack on Iran"In Confront and Conceal: Obama's Secret Wars and Surprising Use of American Power, author David Sanger alleges that Stuxnet...
Cyberweapons: Obama becomes most killing-est president, surpassing Pres. Cheney
Barack Obama "ordered Stuxnet cyber attack on Iran"
Pres. B.S. Obama ordered the viral Stuxnet attack on Iran as part of a wave of cyber sabotage and espionage against the would-be nuclear. It then leaked onto the Internet.
Obama's wave of cyberattacks against Iran
Presidents Bush and Obama behind Stuxnet
Israel and the United States were indeed behind a military-grade computer worm that sabotaged an Iranian nuclear-[power plant] fuel processing facility.
Obama ordered Stuxnet assault on Iran (BankInfoSecurity)
Monday, September 19, 2011
Testosterone Makes the Man
 Sadly most US men suffer from "testosterone poisoning" or they behave like they do. From the example of our political leaders (Clinton's satyriasis, Hillary's lesbianism, Pres. Obama's bisexuality) to the use of toxic plastics and other major sources of xenoestrogens, our hormones are all over the map.
Sadly most US men suffer from "testosterone poisoning" or they behave like they do. From the example of our political leaders (Clinton's satyriasis, Hillary's lesbianism, Pres. Obama's bisexuality) to the use of toxic plastics and other major sources of xenoestrogens, our hormones are all over the map.This hormone disruption is inflamed by hyper-masculinity in video games, sports, music, gun use and, oddly, homosexuality. Sexual misconduct of obsession and acting like wolves leads to indiscriminate behavior with almost any receptive and some unreceptive partner.
 In the military, for example, sexual assault and rape are commonplace. Many of those attacks are male on male. Just as Afghan Pashtuns are accused and condemned for engaging in bacha bazi (dancing boy pederasty/molestation), US soldiers hypocritically engage in similar behavior in the name of top dog pirate/prison machismo. Pirates are famous for the booty they make off with, and they are not the only ones.
In the military, for example, sexual assault and rape are commonplace. Many of those attacks are male on male. Just as Afghan Pashtuns are accused and condemned for engaging in bacha bazi (dancing boy pederasty/molestation), US soldiers hypocritically engage in similar behavior in the name of top dog pirate/prison machismo. Pirates are famous for the booty they make off with, and they are not the only ones.A new report, however, reveals that it is a biological trick. Genes and social training gear men for excessive interest in spreading seeds and making conquests, upping the chances of impregnating someone and spreading those genes. But when the baby comes, dwoop! Testosterone levels drop precipitously -- and with those levels attitudes must change uncomfortably. Suddenly it's my daughter, and I think I know what men are thinking when they look at her. Testosterone makes men, not fatherhood. But NPR disagrees.
 (NPR, Weekend Edition, Sept. 17, 2011) A new study says that when men become fathers, our testosterone levels drop. Like a brick. I doubt that many fathers are surprised. Transcript
(NPR, Weekend Edition, Sept. 17, 2011) A new study says that when men become fathers, our testosterone levels drop. Like a brick. I doubt that many fathers are surprised. Transcript Heidi Klum is the most dangerous celebrity in cyberspace, according to a new list compiled by Internet security developers McAffee. One in ten websites that come up in searches have more than pictures. They have viruses and malware that ruin computers and steal personal information. It is not only supermodels and scandalous actresses. Number 3 on the list is CNN's Larry King replacement Piers Morgan. But most searches are seeking salacious photos of women.
Heidi Klum is the most dangerous celebrity in cyberspace, according to a new list compiled by Internet security developers McAffee. One in ten websites that come up in searches have more than pictures. They have viruses and malware that ruin computers and steal personal information. It is not only supermodels and scandalous actresses. Number 3 on the list is CNN's Larry King replacement Piers Morgan. But most searches are seeking salacious photos of women.- AUDIO: The new Bossa Nova (Alt Latino NPR)
- Get cancer answers without pharmaceuticals or surgery
- PHOTOS: Siddhartha striving in Theravada Indonesia
- AUDIO: When it rains, it spores (Mushrooms in Mass.)
- VIDEO: "Suicidal" mountain cows puzzle police
- Visit the Huntington Library and gardens FREE
- VIDEO: What is nudism and would I like it?
- VIDEO: one of the 10 Most Shocking Animal Attacks Ever
- Defender of Nepalese Gurkhas (who helped British) target of hate
- Panic in India as an 10,000 lb elephant rampages during a religious festival in Kerala (AnimalPlanetTV)
Tuesday, September 13, 2011
Caught in The Web ("Connected" film)
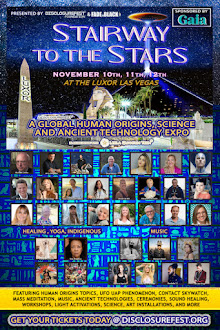
 Buddhist cosmology speaks of devolutions and evolutions and epochs of quiescence and chaos, after Earthlings descended from space (Aganna Sutra), genetic manipulation (usually by nagas in a kind of creationism or celestial intervention), and always more revolutions through the aeons (kalpas in an Indian context of yugas).
Buddhist cosmology speaks of devolutions and evolutions and epochs of quiescence and chaos, after Earthlings descended from space (Aganna Sutra), genetic manipulation (usually by nagas in a kind of creationism or celestial intervention), and always more revolutions through the aeons (kalpas in an Indian context of yugas).US teachings about Evolution vs. Creationism
 How things turn and have turned may only seem comprehensible as envisioned in the Wheel of Samsara, the "continued wandering on" or cycling through rebirths (due to our skillful and unskillful karma) in countless worlds within 31 Planes [broad categories] of Existence.
How things turn and have turned may only seem comprehensible as envisioned in the Wheel of Samsara, the "continued wandering on" or cycling through rebirths (due to our skillful and unskillful karma) in countless worlds within 31 Planes [broad categories] of Existence.But for all that, we still get excited that our mobile device (cell phone) connects us to the Web and lets us tune in and drop out by feeling "connected." Tiffany Shlain is onto something: We are interdependent.

Thursday, June 9, 2011
Macs hit by Malware, iPhones could be next

Unless Apple, Inc. acts fast, Macs are no immune from malware, and iPhones could be hit next. It has taken steps to stop a malware "phishing" program (Image: cutcaster.com).
The ploy, says technology columnist Rich Jaroslovsky of Bloomberg News, uses an infected website to install a piece of software on Apple computers. The software then pops up a new window, with an urgent message about a security vulnerability.
CALLING THE INTERNET POLICE
Hackers Target FBI Affiliate, Post Passwords Online
The hacking collective, Lulz Security, also recently targeted Nintendo, Sony, and PBS.
Nintendo: Server Breached, No Data Lost